CSAW CTF 2015 - Forensics 100 Transfer Writeup

This challenge starts off with the following hint:
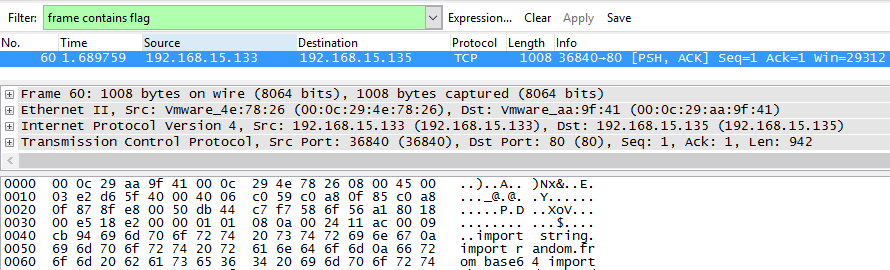
I was sniffing some web traffic for a while, I think i finally got something interesting. Help me find flag through all these packets.This challenge started off with a pcap. Let’s take the cheap way out and do a basic Wireshark filter for frame contains flag: